Catalog
-
Catalog
- Antiquitäten & Kunst
- Auto & Motorrad: Fahrzeuge
- Baby
- Business & Industry
- Bücher
- Camping & Outdoor
- Feinschmecker
- Garden & patio
- Haustierbedarf
- Heimwerken & Garten
- HiFi & Audio
- Home, Construction, Renovation
- Household appliances
- Kleidung & Accessoires
- Modellbau
- Musik
- PC- & Videospiele
- Photo & camcorders
- Sammeln & Seltenes
- Spielzeug
- TV, Video, DVD
- Telekommunikation
- Uhren & Schmuck
- Wellness & Beauty
- computers & electronics
- entertainment & hobby
- fashion & lifestyle
- food, beverages & tobacco
- health & beauty
- institutional food services equipment
- medical equipment, accessories & supplies
- office
- sports & recreation
- vehicles & accessories
- weapons & ammunition
Filters
Search
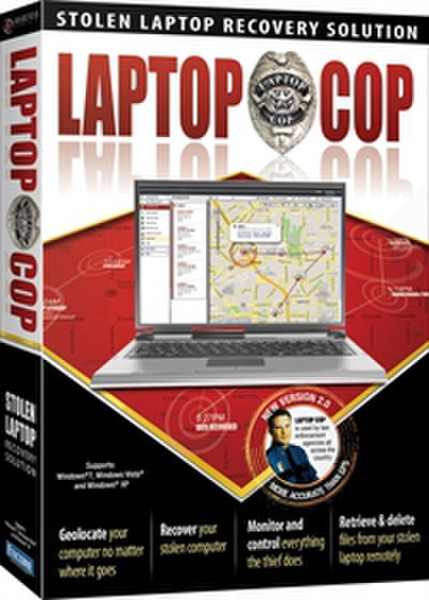
ENCORE Laptop Cop v2.0
MPN: 11991
🚚 Select the country of delivery:
Delivery from:
Germany
Sale and delivery by:
Where to buy and prices (Advertising *)
On Top
Technical specifications
On Top
System requirements
| Minimum RAM | 256 MB |
|---|---|
| Minimum processor | 1GHz |
| Minimum hard disk space | 30 MB |
| Recommended RAM | 512 MB |
Remote Access to Your Stolen Laptop
The ultimate tool to help Law Enforcement recover your laptop and bring the criminals to justice
With so much important information being stored on computers today, recovering the laptop is only one part of the process. For most people, retrieving irreplaceable things like personal files and photos and stopping a thief from viewing private information is even more important. That's where Laptop Cop comes in.
Laptop Cop is an invisible piece of software that gives you secret access to your computer remotely over the Internet no matter where the thief takes the computer. By being able to take control of your computer without the thief's knowledge, a whole world of possibilities beyond just recovering the computer opens up to you
In the event of laptop theft or loss, Laptop Cop's patented technology allows you to geo-locate stolen laptops in real-time. You can also remotely delete/retrieve files from the stolen computer and also monitor and control the thief's every action. We'll also work with law enforcement to recover the physical property.
<b>Features:</b>
- Improved! Geo-locate laptops in real time no matter where an employee or thief goes.
- Improved! Monitor and control everything the thief does.
- Location of laptop plotted on map.
- Geo-location is determined by wi-fi signals, not IP address. Much more accurate.
- Geo-location is more accurate than GPS.
- Remotely delete files from the stolen laptop.
- Get confirmation of deletion of files.
- Deletion done at a US Dept. of Defense standard that ensures complete destruction of the files.
- Remotely retrieve files from the stolen laptop.
- Lock down the stolen laptop if desired.
- Our recovery team works with law enforcement to recover the physical machine.
- Purchaser entitled to 1 year subscription term for service to monitor one laptop.
<b>Additionally:</b>
- Supports different settings for each user of a machine.
- No hardware required.
- Can be used in a Terminal Server or Citrix environment.
- Ties in with Active Directory.
- Quick, easy, and silent deployment with no user prompts if desired.
With so much important information being stored on computers today, recovering the laptop is only one part of the process. For most people, retrieving irreplaceable things like personal files and photos and stopping a thief from viewing private information is even more important. That's where Laptop Cop comes in.
Laptop Cop is an invisible piece of software that gives you secret access to your computer remotely over the Internet no matter where the thief takes the computer. By being able to take control of your computer without the thief's knowledge, a whole world of possibilities beyond just recovering the computer opens up to you
In the event of laptop theft or loss, Laptop Cop's patented technology allows you to geo-locate stolen laptops in real-time. You can also remotely delete/retrieve files from the stolen computer and also monitor and control the thief's every action. We'll also work with law enforcement to recover the physical property.
<b>Features:</b>
- Improved! Geo-locate laptops in real time no matter where an employee or thief goes.
- Improved! Monitor and control everything the thief does.
- Location of laptop plotted on map.
- Geo-location is determined by wi-fi signals, not IP address. Much more accurate.
- Geo-location is more accurate than GPS.
- Remotely delete files from the stolen laptop.
- Get confirmation of deletion of files.
- Deletion done at a US Dept. of Defense standard that ensures complete destruction of the files.
- Remotely retrieve files from the stolen laptop.
- Lock down the stolen laptop if desired.
- Our recovery team works with law enforcement to recover the physical machine.
- Purchaser entitled to 1 year subscription term for service to monitor one laptop.
<b>Additionally:</b>
- Supports different settings for each user of a machine.
- No hardware required.
- Can be used in a Terminal Server or Citrix environment.
- Ties in with Active Directory.
- Quick, easy, and silent deployment with no user prompts if desired.
-
Payment Methods
We accept: