Catalog
-
Catalog
- Antiquitäten & Kunst
- Auto & Motorrad: Fahrzeuge
- Baby
- Business & Industry
- Bücher
- Camping & Outdoor
- Feinschmecker
- Garten & Terrasse
- Haushalt & Wohnen
- Haustierbedarf
- Heimwerken & Garten
- HiFi & Audio
- Home, Construction, Renovation
- Household appliances
- Kleidung & Accessoires
- Modellbau
- Musik
- PC- & Videospiele
- Photo & camcorders
- Sammeln & Seltenes
- Spielzeug
- TV, Video, DVD
- Telekommunikation
- Uhren & Schmuck
- Wellness & Beauty
- computers & electronics
- entertainment & hobby
- fashion & lifestyle
- food, beverages & tobacco
- garden & patio
- health & beauty
- institutional food services equipment
- medical equipment, accessories & supplies
- office
- sports & recreation
- vehicles & accessories
- weapons & ammunition
Filters
Search
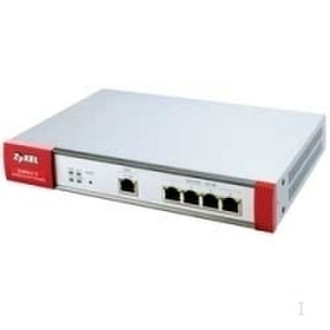
ZyXEL ZyWall 5 UTM Internet Security Appliance 65Mbit/s hardware firewall
MPN: 91-009-014011
🚚 Select the country of delivery:
Delivery from:
Germany
Sale and delivery by:
Mercatos.com
__ live chat shopping ad __ .
.
Imprint / Online Dispute Resolution
Terms of Service
Cancellation policy
Data protection
💳 Payment Methods...
Where to buy and prices (Advertising *)
On Top
Technical specifications
On Top
Data transmission
| VPN throughput | 25 Mbit/s |
|---|---|
| Firewall throughput | 65 Mbit/s |
Networking
| Number of VPN connections | 10 |
|---|
Security
| Content filtering | Java, ActiveX, Cookie, News, URL, IKE + PKI |
|---|
Other features
| Expansion slots | ZyWALL Turbo Card |
|---|
Protocols
| Supported network protocols | PPP, RIP I/RIP II, ICMP, SNMP v1 & v2c + MIB II (RFC 1213), IP Multicasting IGMP v1, v2, IGMP Proxy, UPnP |
|---|
Additionally
| Transfer rate (Mbps) | 100 Mbit/s |
|---|
ZyWall 5 UTM Internet Security Appliance
UTM is an Emerging Trend in Network Security\nGone are the days when a dedicated firewall is sufficient to fend off hackers from cooperate Unified Threat Management (UTM) is an emerging trend in the network security appliance on the cutting edge, ZyXEL’s ZyWALL 5/35/70 UTM series is capable of outperforming 5/35/70 series by up to 20 times with just a ZyWALL Turbo Card. This new technology allinone network security device that provides content filtering, antivirus, antispam and services traditionally handled by multiple systems.\n\nHigh-performance All-in-one Design\nFrom a business perspective, IT managers should consider an “enterprise approach” for security. They can now utilize all-in-one appliances, such as ZyXEL’s 8-in-1 UTM solution, and performance. All of the following features are now offered in one box and controlled unified interface: Anti-Virus, IDP, Anti-Spam, Firewall, VPN, Load Balancing, Bandwidth Content Filtering.\n\nEmpowering ZyWALL Performance with Turbo Card\nTake advantage of secure protection from virus attacks, hackers, and spam. Imagine, about spyware, adware, or other potential threats to your computer and valuable data. safe for your PCs and Network. Upgradeable Design with ZyWALL Turbo Card within 6-Step In an increasingly complex network environment the integrated ZyWALL UTM provides management efforts, easy installation, and multiple layers of network protection.\n\n- High performance with 8-in-1 Security.\n- Exclusive ZyXEL SecuASIC™ accelerating technology.\n- Protection from Spyware, Phishing, Viruses, and Spam.\n- IM (Instant messaging), P2P (Peer-to-peer) Applications, and Granular Control.
-
Payment Methods
We accept: